Virtual Corporation delivers Cyber Security consulting services through personalized engagements that promote quality, collaboration, and ultimately, risk reduction.
The risks and opportunities that digital technologies, devices, and media bring us are palpable. Cybersecurity is never a matter purely for the IT team, despite the fact that they play a vital role in its overall security or lack thereof. An organization’s risk management arm must have a thorough understanding of the constantly evolving risks associated with cybersecurity, as well as the practical tools and techniques that are available to address them when the moment arises.
Cybersecurity could mean financial loss, a disruption, or even worse — irreparable damage to the reputation of an organization because of a failure to its IT systems. Virtual Corporation understands that cybersecurity preparation and data breach planning are a necessity in today’s technology-fueled business world and so we can help you and your teams with planning, implementation, and testing of those plans to ensure your company remains strong and your reputation intact.
So, what is a cybersecurity consultant team?
The definition of the word or term ‘security consultant’ is a bit more extensive, but a part of the description is already in the name. Characteristically, it is a person tasked with identifying the flaws in the information technology system of a company. Moreover, they find better solutions for problems and data breach planning that are becoming difficult to deal with. A cybersecurity consultant will propose specific tech products and apps. Mainly they will put a stop to the issues from reoccurring and, therefore, avoid malicious attacks and theft.
Cyber security consulting services will help you design and implement a plan to prevent any security breaches of your system. This will reduce legal and financial consequences by preventing or minimizing threats, as well as ensuring that they are dispensed with as quickly and seamlessly as possible
Areas of Expertise:
- Cybersecurity Program Coaching
- Outsourced Cybersecurity Program Management (CISO in a Box)
- Cybersecurity Program Maturity Assessment
- Cybersecurity Program Design
- Cybersecurity Risk Assessment Design and Completion
- Data Breach Planning
- Data Breach Exercising
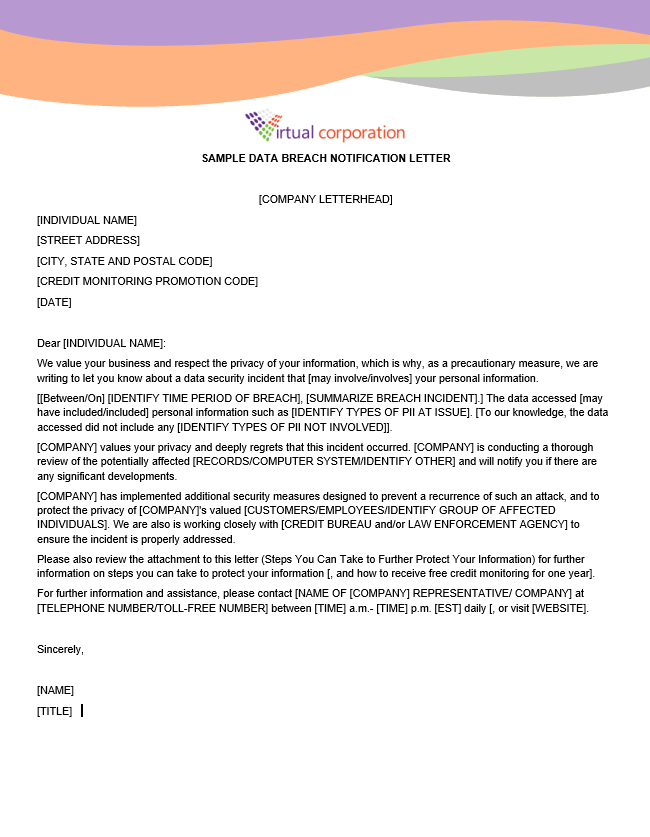
Click on the top right-hand side of this page to download
Sample Data Breach Notification Letter
Disclaimer: The information provided in this sample notification letter has been created by Virtual Corporation to help guide you when creating your own documents. This information provided by Virtual Corporation does not constitute legal, medical, or any other professional advice.
Not all threats come from undetermined criminals, so security consultants avoid both internal and external hazards. Sometimes the planning of data breaches comes from even the most trusted employees within a company. These lawbreakers are able to bypass the enforced exterior defenses. On the contrary, external attacks must crack outer barriers to control the company’s central database.
Cyber threats have become one of the most common dangers to organizations of every industry in this day and age, so it would be a colossal mistake not to take every precaution to avoid becoming a victim and losing valuable information, including your clients, which would be very hard to recover from. Don’t let yourself become a target. We provide all-encompassing cybersecurity consulting from our team of experts and ensure your organizational resilience.
Our proven Cybersecurity Review encompasses the following necessary components to achieve a successful Cybersecurity Practice:
- Security Awareness
- User Data Control
- Data Classification
- Encryption
- Risk and Technology Defenses
- Logging and Monitoring
- Penetration and Vulnerability Testing
- Incident Response Plan (IRP)
- Disaster Recovery
Through cyber security consulting services, you will be able to arrange and execute your business plans efficiently and quickly. You will learn how to prioritize master plans and assess what you can do by yourself and where you need help. Besides extending your business more efficiently and safely, you will also see either tactical or strategic improvements. Moreover, you will learn the importance of data breach planning, strategic roadmaps, and maturity assessments.
Currently – what is a strategic roadmap? Putting it plainly, it is a time-based plan that will help you understand where your business wants to go & how you can get there. It is a category of visual representation that organizes essential statistics for goal planning. In contrast, a maturity assessment helps the user choose if a specific strategy is suitable for the business. This tool recognizes a company to qualify better leads, basing their standards on responses to questions within the assessment, therefore testing them to see if they are ready for the job.
Maturity assessments provide accurate data breach planning, reviews for the people, processes, and technology in your office or workstation – showing how the investments you made in cybersecurity are expanding and developing. It also shows how this growth impacts your business: namely, by minimizing many risks and data breaches. Cyber security consulting services provide each of these items – from work performance, maturity assessment, and the success of the right strategic roadmap.
Contact us today to learn more about our Cyber Security consulting services and how we can help you begin one or improve on the one you have. Our approach is very one-on-one. We want to be your one-stop shop for all things Cybersecurity. We won’t pigeon-hole into one format. We know every organization is unique and requires individual assessment and implementation, there is no such thing as one size fits all when it comes to addressing today’s cyber threats.